

 Read Time: 2mins
Read Time: 2mins  Published: 24/04/2026 | Updated: 24/04/2026
Published: 24/04/2026 | Updated: 24/04/2026 Scaling the Substantial Gap
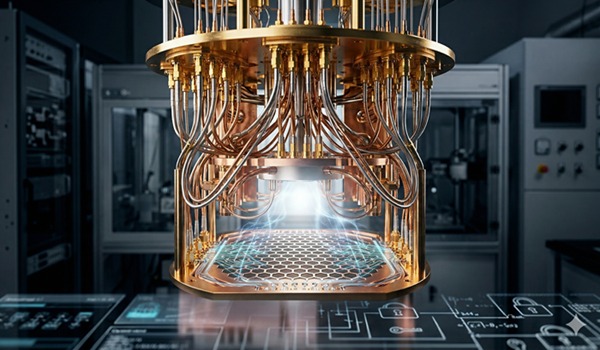
Until recently, the practical application of Shor’s algorithm—a mathematical formula capable of decrypting the Elliptic Curve Discrete Logarithm Problem (ECDLP)—remained largely theoretical.
The previous public milestone was set only seven months ago in September 2025, when engineer Steve Tippeconnic broke a 6-bit key using IBM hardware. Lelli’s success represents a 512-fold increase in complexity in less than a year.
What makes this breakthrough particularly notable is the accessibility of the tools used. Lelli did not rely on secretive government labs or multi-billion-dollar infrastructure; instead, he utilized commercially available quantum hardware via the cloud.
This suggests that the barrier to executing such attacks is lowering, transforming the quantum threat from a problem of fundamental physics into one of manageable engineering.

Assessing the Trillion-Dollar Risk
The implications for the digital asset market are profound. Current estimates suggest that over $2.5 trillion in wealth is protected by Elliptic Curve Cryptography (ECC). Specifically, about 6.9 million Bitcoins are stored in legacy addresses where public keys are already visible on the blockchain.
This includes the legendary million-BTC fortune attributed to Satoshi Nakamoto. Because these keys are already exposed, they are sitting ducks for any sufficiently powerful quantum processor.
Recent academic shifts have also heightened the sense of alarm. A Google Research paper published in early 2026 suggested that a 256-bit Bitcoin key could be compromised by roughly 500,000 physical qubits.
More recent findings from Caltech have revised that figure down even further, suggesting that specialized architectures might require as few as 10,000 qubits to bypass current security measures.
A Race Toward Post-Quantum Standards
While some market analysts, including those at Bernstein, argue that quantum computing remains a medium-term concern rather than an immediate crisis, developers are not waiting to find out.
The Bitcoin community is currently evaluating several Post-Quantum proposals.
These include BIP-360, which aims to introduce a quantum-hardened transaction format, and BIP-361, a more aggressive measure that would phase out older, vulnerable systems and potentially freeze assets that fail to migrate to new standards.
As the industry watches the “Q-Day Prize” benchmarks move higher, the consensus is shifting.
The question is no longer whether quantum hardware will reach the 256-bit threshold but how quickly the decentralized world can rewrite its own DNA to survive the transition.
 Fact checked by
Fact checked by 




 eabungana@gmail.com
eabungana@gmail.com 
